Cybercrime is a growing problem that is critical for businesses to be aware of and to implement measures against. As digital technologies continue to evolve and become used in most aspects of people’s personal and professional lives, awareness of cybersecurity is more important than ever before.
According to Cybersecurity Ventures, the global cost of cybercrime reached $10.5 trillion in 2025 and is projected to climb to $12.2 trillion annually by 2031.
Cybersecurity awareness for employees is one of the most important things you can deliver in the fight against cybercrime and to help protect your business.
Table of contents
What is cybersecurity awareness?
Why is employee cyber security awareness important?
How to improve employee cyber security awareness
How to increase employee cybersecurity awareness with DeskAlerts
What is cybersecurity awareness?
Cybersecurity awareness is an educational measure that businesses can conduct internally to teach their employees about different types of cyber threats, how to detect them and what to do if they have made a mistake.
Employees are the number one cause of cybersecurity incidents in organizations, usually as a result of human error.
By sending frequent communications including cyber security tips for employees, reminders and quizzes, you can help to create a culture of cyber security and cyber security threats front-of-mind. Employees will understand the risks as well as the consequences of cybersecurity threats.
Case study: How University Hospitals Birmingham NHS Foundation Trust managed to protect its system during a cyberattack.
Why is employee cybersecurity awareness important?
Your employees are the driving force of your organization and are responsible for carrying out the day-to-day activities that help it run. In doing this, they have roles that include handling important and/or sensitive data as well as interacting with various stakeholders.
When they fail to properly protect company data, there can be a wide range of serious problems for the company. This can include:
- Regulatory issues, such as failing to protect information under the General Data Protection Regulation (GDPR), which can lead to massive fines
- Reputational damage with customers and other stakeholders losing trust in your brand
- Disruption to your operations, which could cause major losses
- Loss of confidential data and sensitive fines
- Loss of money, particularly if the criminals are able to access company banking accounts
6 Cybersecurity Email Templates [+ Tips]
Increase Message Visibility and Prevent Cybersecurity Breaches. Download for free

How to improve employee cyber security awareness
Taking the time and effort to overhaul and improve cybersecurity awareness is one of the best decisions you can make for your business, and any expense that you incur is likely to be a wise investment.
Read also: Raising Cybersecurity Awareness in Healthcare
1. Budget for cybersecurity awareness
No matter what technological measures you spend money on to protect your systems from cyber attacks, it could all be for nothing if you don’t match it with appropriate awareness and training aimed at your employees – after all, if they don’t understand that they have a role to play in keeping your systems safe, they are more likely to fall prey to any number of cyber attacks or other scams. Set aside money in your cybersecurity budget to train up your staff on an ongoing basis.
2. Consider security awareness for employees as a risk mitigation strategy
When you take a risk-based approach to managing cybersecurity in your organization, you need to create a hierarchy of risks to security and then create mitigation strategies for each. Given that employees are one of the biggest weaknesses in a company when it comes to security risks, cybersecurity awareness is a strategy that needs to be deployed in order to help neutralize this risk.
3. Model appropriate behavior from the top down
It is important that those in leadership roles within your company model the behavior that you expect employees to display. This sets the tone for the whole company, and your leadership team becomes champions of cyber security awareness for employees.
What are the key cyber risk management components?
Watch this video from our cybersecurity webinar
(speaker - Craig Rosewarn, MD of Wolfpack Information Risk)
4. Include cybersecurity training in your onboarding process
When new employees join your company, you should provide them with appropriate cybersecurity training so that they know what is expected of them from the very first time they use a company computer on the corporate network. This includes pointing out specific threats to be aware of and telling them about the risks and consequences of not following the appropriate protocols.
5. Carry out refresher training
Don’t make training and awareness a one-time deal. It should be a requirement that employees undertake awareness training at least annually and should also be tested on their knowledge.
6. Inform employees about new and emerging threats
Cybercriminals become more and more sophisticated all the time and often find new and improved ways to find vulnerabilities and weaknesses that they can exploit to get access to credentials, data and money. When new threats emerge, it’s important that you let employees know about them as they occur – don’t wait for annual refresher training to promote awareness of cybersecurity.
6 Cybersecurity Email Templates [+ Tips]
Increase Message Visibility and Prevent Cybersecurity Breaches. Download for free

7. Target your training to people with specific roles and functions
When there are vulnerabilities and weaknesses identified with specific roles, or with particular software systems, it makes sense to only deliver targeted training about these issues with the employees who aку affected. Otherwise, you are sending irrelevant and potentially confusing, complex information to people who do not need to receive it.
8. Make sure your training and advice are easy to understand
Most of the people in your organization are unlikely to be IT experts, so don’t communicate with them in highly complex, technical jargon that they are unlikely to understand. Send any information in simple, concise, easy-to-understand language.
9. Run an internal marketing campaign
A good way to promote your cyber awareness program is to market it to employees in the same way you may market a product to the external world. This can include developing branding – a ‘look and feel’ to your material that is consistent and easily identifiable. You can then deliver the information in different ways using that collateral.
How to increase employee cybersecurity awareness with DeskAlerts
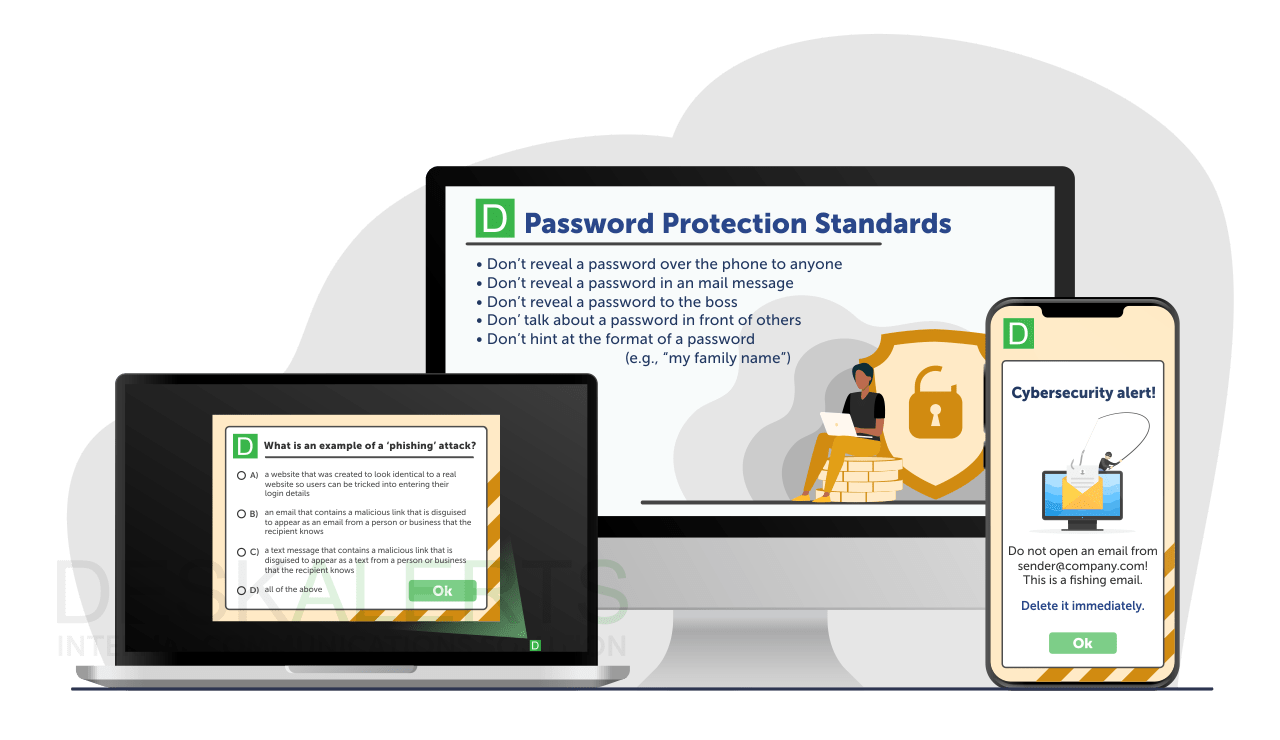
DeskAlerts is an internal communication software system that comes complete with a wide range of channels and tools and can be used to increase cyber security awareness within your organization by using it in the following ways:
1. Awareness communications
This is the stage of cybersecurity awareness where you teach employees about different threats and how to identify them, as well as provide cybersecurity tips for employees – essentially guidance on what steps to take and how to behave.
6 Cybersecurity Email Templates [+ Tips]
Increase Message Visibility and Prevent Cybersecurity Breaches with DeskAlerts. Download for free

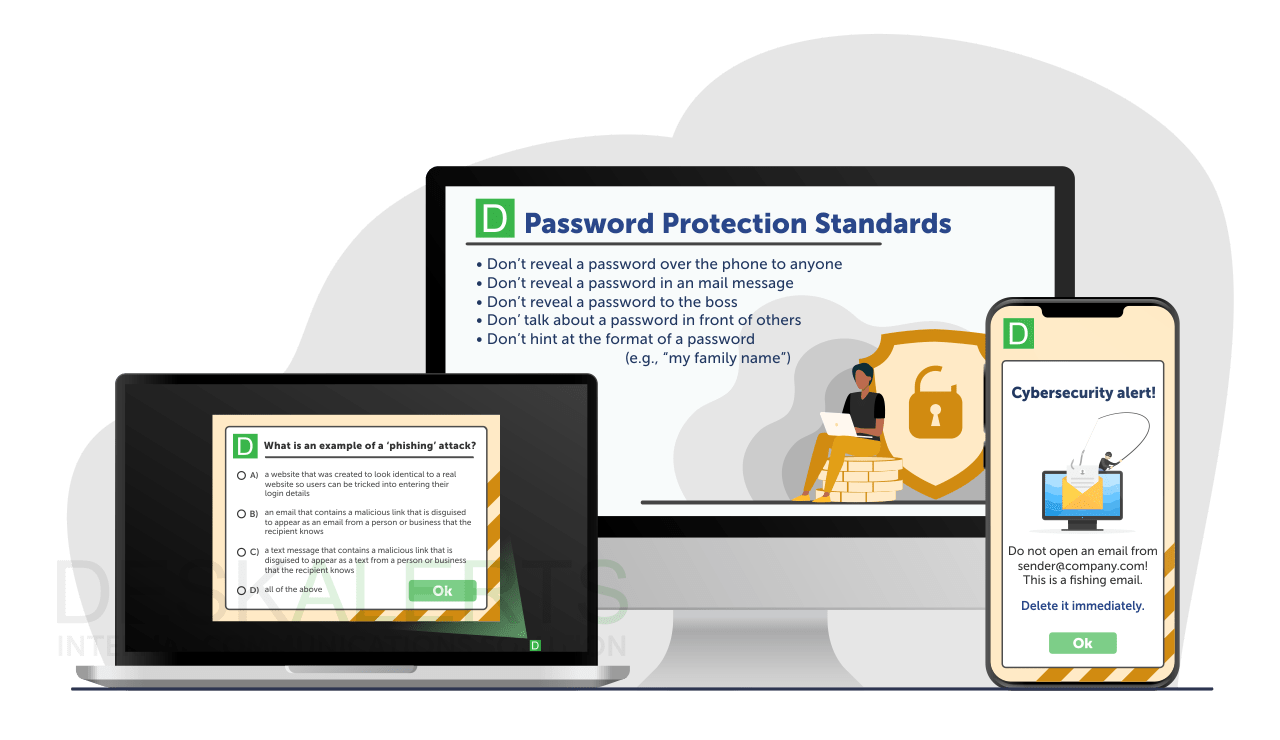
This can be achieved by using DeskAlerts tools such as pop-up notifications, desktop tickers, corporate wallpapers, corporate screensavers and digital signage to deliver hints, tips and reminders.
You can also send people pop-ups with video content that provides more in-depth training and can follow this up with quizzes to test your employees’ knowledge.
It’s important to get the balance right and inform people while not bombarding them too much so that they are distracted from their usual work or cease to pay attention. With DeskAlerts, you can measure your engagement to determine how much people have paid attention.
How to use corporate lockscreen to remind employees about secure login practices?
Watch this video from our cybersecurity webinar
(speaker - Roman Toporkov, CTO of DeskAlerts)
2. Crisis management communications
This stage of communication takes place when there is a breach or another cybersecurity incident. It relies on sending urgent/critical communication to employees, informing them about the issue and providing instructions about what steps they need to take.
Because of the nature of these communications, it is important that the information you send is highly visible. The stakes are extremely high during a cybersecurity breach: you stand to incur significant losses as a business.
Sending information quickly and in a way that cannot be ignored is essential – and DeskAlerts has the appropriate tools for this job.
Pop-up notifications can be sent to computer screens in a way that can’t be ignored or skipped and will appear regardless of whatever other apps or software the employee is using. Pop-ups can even be sent that take up the whole screen, and if you need to you can prevent people from using their computers to minimize any damage.
With so many distractions and digital noise and information overload, you need systems that are more reliable than just sending cybersecurity awareness emails to employees.
The desktop ticker will be a handy tool for updating staff about the current situation. It is highly visible but does not cause unnecessary distractions.
3. Aftermath analysis of communications
Once the cybersecurity issue has been resolved and you are carrying out business continuity measures within your organization, you can turn your thoughts to how well your crisis communications and awareness communications worked. What went well? What went wrong?
One of the best ways to approach this is to send surveys to identify pain points and what you will need to address in the future. With DeskAlerts, you can send surveys in a way that provides you with results in real time so that you don’t have to wait for weeks to get feedback.
***
Cybersecurity communication is more than just sending out security awareness tips to employees: regular communication and training can help to build a culture of security within your organization that can help to ensure your cyber resilience.
6 Cybersecurity Email Templates [+ Tips]
Increase Message Visibility and Prevent Cybersecurity Breaches with DeskAlerts. Download for free

Frequently Asked Questions
How do you promote awareness on cybersecurity?
To promote cybersecurity awareness, it’s important that everyone in the organization, from the top down, understands the role they have to play in keeping your company’s systems and data safe. They need to be made aware of the specific threats that the organization faces, and what steps they need to take to prevent breaches.
How can security awareness be improved?
Regularly reviewing your cybersecurity protocols, as well as the overall threat landscape and employee preparedness, can help drive constant improvements to security awareness. This will help you identify any gaps or weaknesses in your cyber awareness programs, and you can then make appropriate changes to ensure your employees are regularly updated on the information they need to help keep your systems safe from cyberattacks.
How do you create a culture of security awareness?
Emphasizing the importance of security awareness from the top down in your organization helps to create a culture of security awareness. When your leaders set the example for the staff, it helps them understand the importance of security. Taking other measures to keep security front of mind will help to reinforce this – for example, sending frequent communications, talking about it in team meetings, and running internal marketing campaigns.
How do you create cyber awareness?
You can create cyber awareness in your organization by taking the following steps:
- Ensure you have gained buy-in and participation from the leadership team
- Create your content and send cybersecurity tips for employees in an engaging and personalized way
- Provide training on the types of threats employees need to be aware of, such as phishing, ransomware, company password policy, etc.
- Quiz your employees and test their knowledge
- Provide refresher training annually.
 Caroline Duncan
Caroline Duncan